Secure by design
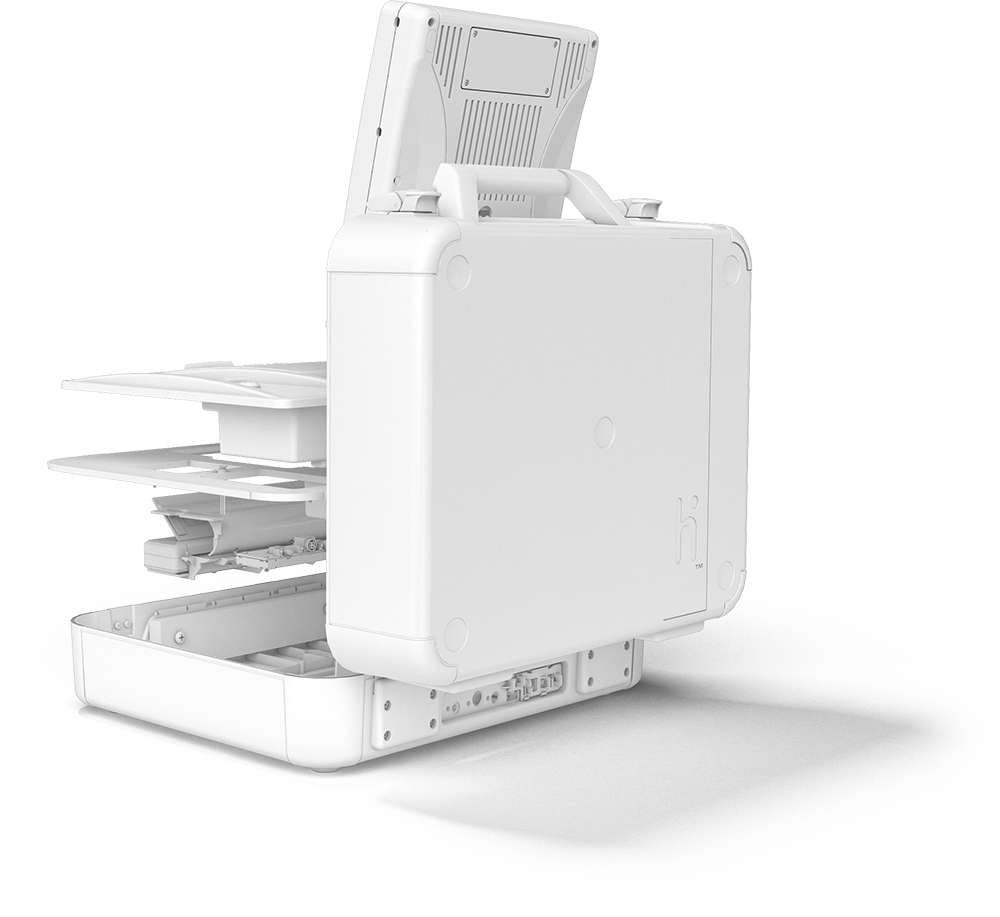
Verity employs a unique "Defense in Depth" approach across the entire product line.
This means we implement multiple layers, and types, of security controls to maximize defenses and eliminate gaps between protections.
It starts with development. To be a truly secure product, the environment in which it is created must also be secure. Hart follows the Secure Development Framework set forth by the National Institute of Standards and Technology (NIST).
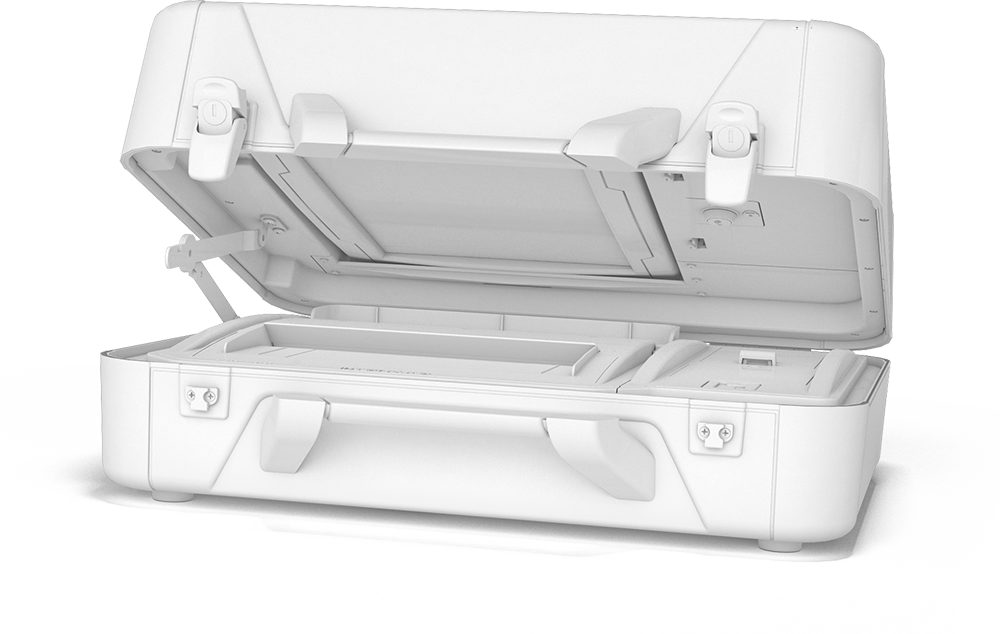
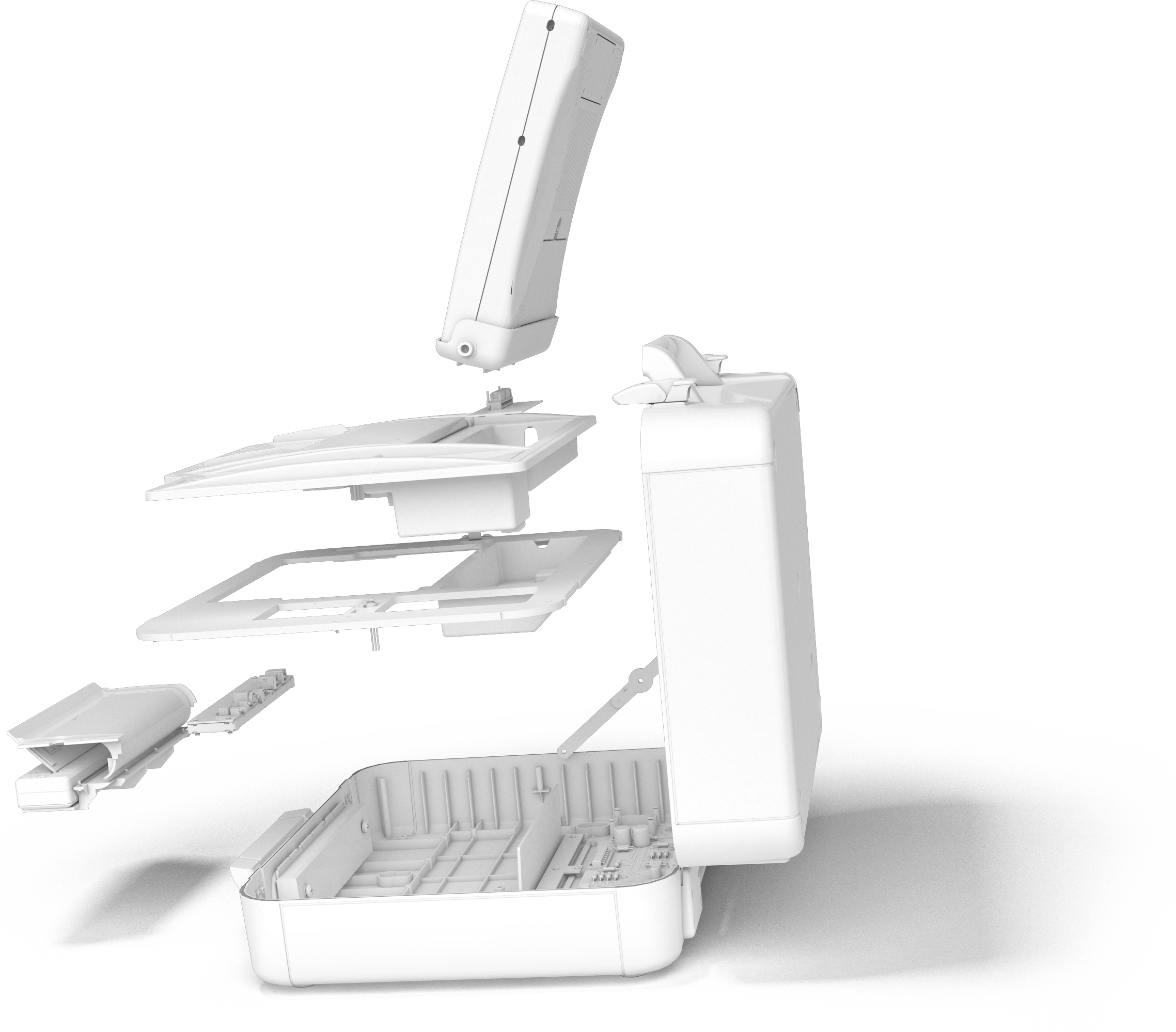
Risk is designed out of the system by keeping different parts of the voting process separate. For example, election data is in a secure, protected location on the devices, separate from power buttons or other poll worker facing controls.

Verity's physical access controls include layers of keyed locks, features to support the use of effective tamper-evident seals, and more.
Digitally signed audit logs and cast vote records are stored in multiple redundant locations, ensuring no loss of data and easy detection of any attempts to manipulate data.

Unlike other voting technologies that use “hardened” commercial operating systems, Verity uses the same secure embedded technology found in critical infrastructure. Embedded operating systems are used for purpose built, single function technologies. There is no need to “turn off” unnecessary functionality (like internet connectivity).
Secure Boot ensures that your Verity system starts up using only firmware that is trusted by Hart. The system will not turn on if the firmware has been tampered with in any way.

Rather than trying to block each new threat, Verity only allows pre-approved software. Any unauthorized programs or software are rejected, and the system is protected from any attempts of modification. This application "trust-listing" is unique to Verity.
Verity uses military grade encryption to protect election data. Encryption keys, or "how you crack the code", are automatically changed for every election.
All Verity Voting technology runs in a secure “kiosk” mode that disallows user access to the operating system of the voting device or in-office workstation. This is unique to Verity.
Verity provides a 100% voter verifiable paper trail that tabulates votes from the same words the voter verified, not a black box barcode
Verity provides additional protection with robust password management options. Users can set rules for complexity, expiration, password reuse, account lockouts, and more.
Two-factor authentication is required to ensure access to critical functions is limited to authorized users.

Role-based profiles guarantee that users may only access those parts of the system which they need to do their job.
Verity includes a sliding door system to protect communications ports in the back of devices. This patented innovation enables tamper evident seals that are easily managed by poll workers.

Non-standard ports & wiring prevent unauthorized users from using standard, commercial-off-the-shelf cables or devices into Verity voting machines. If you plugged a normal USB stick into a Verity device, it would not register
The Verity Voting system delivers the most secure election technology available - designed, developed, and manufactured right here in the United States of America.


